This week we’re going to further try and bypass the Windows Defender antivirus – the bare minimum for our project. I’ve come across a couple of good leads:
- First, change the connection port number to something less obvious, like 8080.
- There is a very promising program we could use called herpaderping (more on this here), but it takes away from the easy-to-execute principle… perhaps a plan B?
- Some testing with pyarmor
- Further code evasion tricks (we already have one implemented)
Let’s start with the easy, which is changing the port numbers… 8080 is a port that shouldn’t arouse any suspicion since it is commonly used when using the web. Random TCP ports like 4444 are more likely to be thwarted.
Next, I wanted to try pyarmor. There is a pretty easy way to use it in our case, here’s the docs. Pretty low expectations for that one though. To install, just type pip install pyarmor in your terminal, very straightforward. Next, let’s refer to the docs I linked earlier and use pyarmor to pack and execute the python file. I also had to run the program from where it installed, but all of our plans were foiled by this error message:
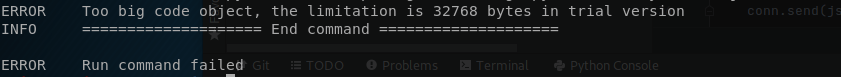
Looks like we’ll have to pay up to use this program, which obviously is not happening.
I’ve also looked into other options other than pyinstaller due to the fact that it might be pyinstaller that is triggering Windows Defender and not my program: Windows Defender never complains if I run my .py file from the command line, although that might be normal behavior.
Breakthrough
So let me preface this by telling you that I am indeed running tests without always reporting them: I don’t believe tedious content is something I should spend my time writing here. But let me do a quick overview of what I’ve done, because I’ve just bypassed Windows Defender:
- Changed port to 8080 (talked about this before)
- Changed pynput version to 1.6.8 (for pyinstaller compatibility)
- Created a new exe called “omena_ohjelma.exe” (apple_program in english). It’s the same .exe I’ve created before (well, not exactly, there is new code but still).
And to my great surprise, this just works. Windows Defender does not catch our program (although it does warn us multiple times: are you sure you want to run this? This is because it’s coming from an unknown publisher). This was tested on both of my Windows 10 virtual machines AND my host machine. This means we’ve successfully bypassed Windows Defender. What is so different from last time? I’m not sure. But we did it, and honestly, that’s all that matters to me.
Quick demonstration video that proves that this is working: https://www.youtube.com/watch?v=0wkfWlW24YU
Notice that I do have the “send automatic samples” setting turned off. We don’t want our file to get analyzed and countered, after all. That would be a major waste of time. And I’m not expecting this program to evade AV long in the future: it’s a constant cat and mouse game. However, this video is proof that as of today, our program does what it is supposed to.
This weeks report was quite short despite the fact that I did spend a considerable amount of time working on the project. As I mentioned, 85% of what I’ve done has not been reported here for not being report-worthy (mostly googling possible solutions before finally trying a bunch of stuff out). Just know that there was something behind the scenes here. Anyway, next week we’ll be finishing this project. See you then!
Caius Juvonen